The 3 Russian cyber-attacks the West most fears

US President Joe Biden has called on private companies and organisations in the US to “lock their digital doors”, claiming that intelligence suggests Russia is planning a cyber-attack on the US.
The UK’s cyber-authorities are also supporting the White House’s calls for “increased cyber security precautions”, though neither has given any evidence that Russia is planning a cyber-attack.
Russia has previously stated that such accusations are “Russophobic”.
However, Russia is a cyber-superpower with a serious arsenal of cyber-tools, and hackers capable of disruptive and potentially destructive cyber-attacks.
Ukraine has remained relatively untroubled by Russian cyber-offensives but experts now fear that Russia may go on a cyber-offensive against Ukraine’s allies.
“Biden’s warnings seem plausible, particularly as the West introduced more sanctions, hacktivists continue to join the fray, and the kinetic aspects of the invasion seemingly don’t go to plan,” says Jen Ellis from cyber-security firm Rapid7.
Here are the hacks that experts most fear.
BlackEnergy – targeted critical infrastructure attack
Ukraine is often described as the hacking playground of Russia, which has carried out attacks there seemingly to test techniques and tools.
In 2015 Ukraine’s electricity grid was disrupted by a cyber-attack called BlackEnergy, which caused a short-term blackout for 80,000 customers of a utility company in western Ukraine.

Nearly exactly a year later another cyber-attack known as Industroyer took out power for about one-fifth of Kyiv, the Ukrainian capital, for around an hour.
The US and EU named and blamed Russian military hackers for the attacks.
“Russia could absolutely try to execute an attack like this against the West as an illustration of capabilities and to make a statement,” says Ukrainian cyber-security responder Marina Krotofil, who helped investigate the power-cut hacks.
“However, no cyber-attack against a power grid has resulted in an extended interruption of power supply. Executing cyber-attacks on complex engineering systems in a reliable way is extremely difficult and achieving a prolonged damaging effect is sometimes impossible due to in-built protections.”
Experts like Marina also hypothesise that this could backfire on Russia too, as the West most likely also has a decent foothold in Russian networks too.
NotPetya – uncontrollable destruction
NotPetya is thought to be the most costly cyber-attack in history and has been blamed on a group of Russian military hackers by the US, UK and EU authorities.
The destructive software was hidden in an update of popular accounting software used in Ukraine, but spread worldwide destroying the computer systems of thousands of companies and causing approximately $10bn of damage.
North Korean hackers are accused of causing huge disruption with a similar attack a month earlier.
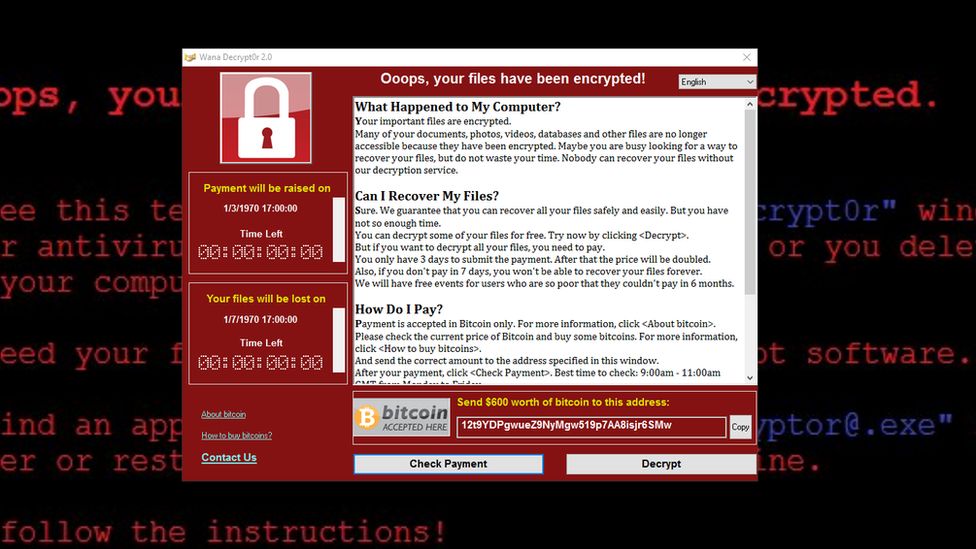
The WannaCry “worm” (a kind of virus) scrambled data on approximately 300,000 computers in 150 countries. The UK’s National Health Service was forced to cancel large numbers of medical appointments.
“These kinds of attacks would cause the greatest opportunity for mass chaos, economic instability, and even loss of life,” says Jen Ellis.
“It might sound far-fetched, but critical infrastructure often depends on connected technologies just as much as every other part of our modern lives and we have seen the potential for that with the impact of the WannaCry on UK hospitals.”
However, computer scientist at the University of Surrey Professor Alan Woodward says such attacks carry risks for Russia too.
“These types of uncontrollable hacks are much more like biological warfare in that it’s very difficult to target specific critical infrastructure in specific places. WannaCry and NotPetya saw victims in Russia too.”
Colonial Pipeline – cyber-criminal attacks intensify
In May 2021 a state of emergency in a number of US states after hackers caused a vital oil pipeline to shut down.

Colonial Pipeline carries 45% of the East Coast’s supply of diesel, petrol and jet fuel and the supply led to panic at the gas pumps.
This attack wasn’t carried out by Russian government hackers, but by the DarkSide ransomware group, which is thought to be based in Russia.
The pipeline company admitted to paying criminals $4.4m (£3.1m) in hard-to-trace Bitcoin, in order to get computer systems back up and running.

A few weeks later meat supplies were impacted when another ransomware crew called REvil attacked JBS, the world’s largest beef processor.
One of the big fears experts have about Russian cyber-capabilities is that the Kremlin may instruct cyber-crime groups to co-ordinate attacks on US targets, to maximise disruption.
“The benefit of instructing cyber-criminals to carry out ransomware attacks is the general chaos they can cause. In large enough numbers they can cause serious economic damage,” Prof Woodward says.
“It also comes with the added bonus of plausible deniability as these groups are a step removed from an attack by the Russian state.”
How could the US respond?
In the highly unlikely case that a Nato country is on the receiving end of a cyber-attack that causes loss of life or huge irreparable damage, then this could trigger Article 5, the alliance’s collective defence clause.
But experts say this would drag Nato into a war it does not want to be a part of, so any response is more likely to be from the US and close allies.
President Biden has already said that “we are prepared to respond” if Russia launches a large attack on the US.
However, the unprecedented cyber-chaos seen in Ukraine in recent weeks from vigilante hackers on either side of the war shows how easily things can escalate. So any action is likely to be extremely carefully considered.
This video can not be played

