Kenya cyber-attack: Why is eCitizen down?

Kenya’s government has been fighting off a huge cyber-attack that has affected services on a key government online platform for almost a week.
The attack has also affected some private companies, although the extent is not yet clear.
There are still questions over who was behind it and what was the motive.
What has happened?
The government has confirmed that there was a cyber-attack on the eCitizen portal, used by the public to access over 5,000 government services.
This was after people complained for several days over difficulties accessing services on the portal, including:
- Passport applications and renewal
- Issuing e-visas for foreigners visiting the country
- Issuing driving licenses, identification cards and national health records
The government was forced to promise visas on arrival for visitors who would have qualified for e-visas due to the challenges with the eCitizen system.
There were also disruptions to train-booking systems and payment for electricity.
Mobile-money banking services were also affected and people relying on the popular mobile-money service M-Pesa to make payments at shops, public transport vehicles, hotels and other platforms also experienced difficulties.
Safaricom, which operates the service, is yet to officially comment and it is not clear whether the company was affected by the hack.
What’s the impact?
The government has been pushing people to use online government services, and this, coupled with the widespread adoption of mobile money payments, meant many Kenyans felt the impact of the attack.
Some 76% of Kenyans use mobile money, while 67% use the mobile internet.
Confirming the attack, Information, Communication and Digital Economy Minister Eliud Owalo stressed that no data had been accessed or lost, although the hackers behind it had claimed to have stolen passport data.
Senior ministry officials on Friday held a meeting with private sector players to discuss issues about cyber security, although it is not clear whether this was triggered by the attack, or had been pre-planned.
The government says it has managed to block the source of the attack although intermittent interruptions continue to affect the normal speed and access of services on the online platform.
Who was behind the attack?
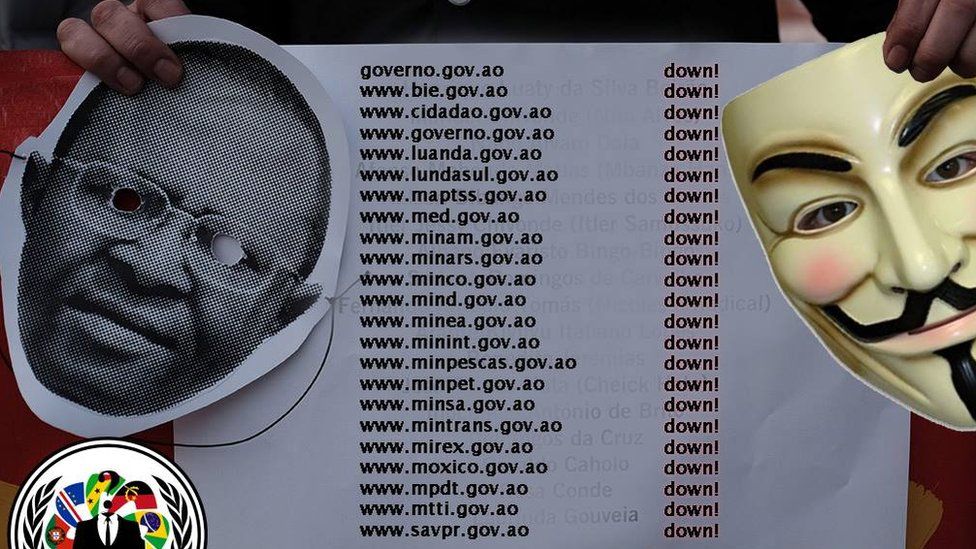
A group calling itself Anonymous Sudan has claimed responsibility.
It portrays itself as a group of Sudanese cyber-warriors and has sworn to attack anyone who tries to interfere in the internal affairs of Sudan, but it is believed to have links to Russia.
The group outwardly supports Russia and has become an affiliate of the pro-Russian hacking group Killnet. It denies having links to the famous international hacktivist collective – Anonymous.
Anonymous Sudan emerged in January this year and has become extremely prolific, carrying out regular attacks that can be classed as disruptive but not sophisticated.
The group has mostly been posting its messages on a Telegram channel where a warning of an impending attack on Kenyan systems was posted on Sunday.
It says it attacked the country because “Kenya has been attempting to meddle in Sudanese affairs and released statements doubting the sovereignty of our government.”
The Sudanese government has frequently rejected Kenyan President William Ruto’s attempt to mediate in the ongoing conflict between the Sudanese military and the paramilitary Rapid Support Forces (RSF), accusing him of lacking neutrality.
Last week a video showing a Sudanese general taunting President Ruto and the Kenyan army went viral online.
Then a member of parliament belonging to Mr Ruto’s party recorded a video, which was also widely shared, hitting back at the general.
Last month BBC Cyber Correspondent Joe Tidy interviewed a representative of Anonymous Sudan over Telegram along with a cyber researcher called IntelCocktail.
The group denied having links to Russia.
“Those claims are all baseless and false, we sometimes write in Russian simply because there are many Russian members in our channel,” the spokesperson said.
However, a report by cyber-security provider Truesec, released earlier this year, highlighted that Anonymous Sudan’s Telegram account lists its user location as Russia.
Researchers from cyber-security companies like Mandiant and Trustwave suggest the group could be working with or for the Kremlin but neither has proven it.
In June, during the Wagner mutiny, the group declared its support for the Kremlin.
They explained it this way: “We don’t care or focus on Russian affairs, but a similar thing happened to our country, and Russians stood with us, so we wanted to pay them back.”
Joe Tidy said it wasn’t possible to draw any firm conclusions about the group’s true identity from the interview.
How was the attack carried out?
It was mainly a DDOS (Distributed Denial of Service), a tried and tested method used by hackers to flood online services with traffic in an attempt to overwhelm the system and cause it to go offline.
Anonymous Sudan used the same method in their attack against Microsoft services in June, their most high-profile previously.
“They tried jamming the system by making more than ordinary requests into the system. It started by slowing down the system,” said the Information Minister.
Bright Gameli, a Kenya-based cyber-security expert, believes insiders could be involved.
“DDOS to critical endpoints are never random. One needs to know a lot of information to know exactly where to hit, thus bringing a lot of systems to a halt,” he said.
“We are lucky there hasn’t been any exfiltration of data because that would have been embarrassing.”
Related Topics
-
-
30 March 2016
-
-
-
18 July 2013
.jpg)
-

