Hundreds of companies potentially hit by Okta hack

Hundreds of organisations that rely on Okta to provide access to their networks may have been affected by a cyber-attack on the company.
Okta said the “worst case” was 366 of its clients had been affected and their “data may have been viewed or acted upon” – its shares fell 9% on the news.
It says it has more than 15,000 clients – from big companies, including FedEx, to smaller organisations, such as Thanet District Council, in Kent.
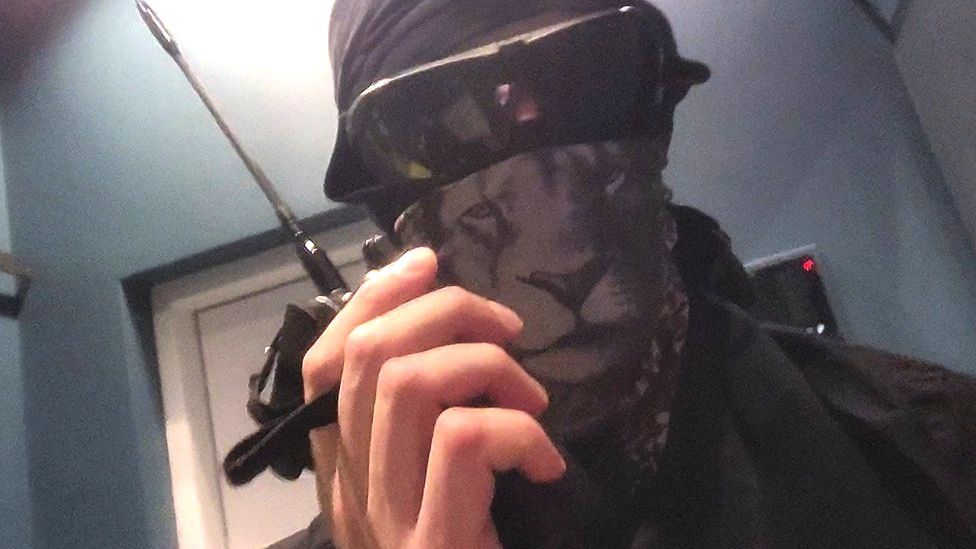
Cyber-gang Lapsus$ is behind the hack.
The ransomware group “is a South American threat actor that has recently been linked to cyber-attacks on some high-profile targets”, according to Ekram Ahmed, of cyber-security company Checkpoint .
“The cyber-gang is known for extortion, threatening the release of sensitive information, if demands by its victims are not made” he said.
The group has previously claimed to have broken into some high-profile companies, including Microsoft.
In a blog post, Microsoft said Lapsus$ had gained only limited access, after compromising a single account, but no customer code or data was involved.
Concern mounted
Okta initially said the attack, in January, involved a third-party contractor, a “sub-processor”, and “the matter was investigated and contained”.
“There is no evidence of ongoing malicious activity beyond the activity detected in January,” it said.
But as concern mounted, Okta published a series of updated blog posts providing more detail.
Chief security officer David Bradbury revealed the hackers had accessed the computer of a customer-support engineer working for the sub-processor, over a five-day period in mid-January.
The attack had been “analogous to walking away from your computer at a coffee shop, whereby a stranger has – virtually, in this case – sat down at your machine and is using the mouse and keyboard”, he said.
But the engineer’s computer had not provided “god-like access”, the hackers had been constrained in what they could do, Okta itself had not been breached and remained fully operational.
“There are no corrective actions that need to be taken by our customers,” Mr Bradbury added.
‘Extreme vigilance’
The contractor employing the engineer, Sykes, part of the Sitel Group, said it was “confident there is no longer a security risk”.
But in collaboration with external cyber-security experts, it would “continue to investigate and assess potential security risks to both our infrastructure and to the brands we support around the globe”.
Lapsus$ said, in online posts, it had not stolen “any databases from Okta” and was focused only on its customers.
None of Okta’s clients has reported any issues – but Mr Ahmed urged “extreme vigilance and cyber-safety practices”.
“The full extent of the cyber-gang’s resources should reveal itself in the coming days,” he added.
Multiple applications
One of Okta’s clients, Cloudflare, said, in a blog post, it did not believe it had been compromised.
FedEx told the Reuters news agency it had “no indication that our environment has been accessed or compromised”.
Thanet, which uses Okta to simplify the way staff manage and sign on to multiple applications, told BBC News the hack “has not compromised the security of the council’s data” but it “will continue to monitor the situation”.
Britain’s National Cyber Security Centre said it had “not seen any evidence of impact in the UK”.